

| Wireless News Aggregation |
|
Welcome Back To
The Wireless
|
NO POLITICS HERE
This doesn't mean that nothing is ever published here that mentions a US political party—it just means that the editorial policy of this newsletter is to remain neutral on all political issues. We don't take sides.
A new issue of the Wireless Messaging Newsletter is posted on the web each week. A notification goes out by e-mail to subscribers on most Fridays around noon central US time. The notification message has a link to the actual newsletter on the web. That way it doesn’t fill up your incoming e-mail account. There is no charge for subscription and there are no membership restrictions. Readers are a very select group of wireless industry professionals, and include the senior managers of many of the world’s major Paging and Wireless Messaging companies. There is an even mix of operations managers, marketing people, and engineers — so I try to include items of interest to all three groups. It’s all about staying up-to-date with business trends and technology. I regularly get readers’ comments, so this newsletter has become a community forum for the Paging, and Wireless Messaging communities. You are welcome to contribute your ideas and opinions. Unless otherwise requested, all correspondence addressed to me is subject to publication in the newsletter and on my web site. I am very careful to protect the anonymity of those who request it. I spend the whole week searching the INTERNET for news that I think may be of interest to you — so you won’t have to. This newsletter is an aggregator — a service that aggregates news from other news sources. You can help our community by sharing any interesting news that you find.
Editorial Opinion pieces present only the opinions of the author. They do not necessarily reflect the views of any of advertisers or supporters. This newsletter is independent of any trade association. I don't intend to hurt anyone's feelings, but I do freely express my own opinions.
HELP SUPPORT THE NEWSLETTER These are uncertain times.
|
||||||||||||
|

|
|
Subscribe Here IT'S FREE * required field
|

|
|
Advertiser Index
|
Service Monitors and Frequency Standards for Sale
(Images are typical units, not actual photos of items offered for sale here.)
|
Passive Audio Amps For Smart Phones
Buy An Amp todayOh come on they are cool.These are acoustic amplifiers for smartphones. They don't need electric power to operate and there are no moving parts. They work like a megaphone (speaking-trumpet, bullhorn, or loudhailer). Everyone that I have shown one to has said something like “Wow, I want one of those!” So I have built a few of them. Of course there are more “Hi-Fi” ways to listen to audio on your smartphone but who would want to plug an elegant smartphone into some cheap, plastic gadget? Or even use Wi-Fi or Bluetooth, which are a pain in the neck to set up, even on a smartphone. These have been made with hardwood bases and some of them are exotic hardwoods with interesting grain patterns. The horns are polished brass — made from mostly old horns that had rubber bulbs on the ends and were used in “times gone by” by taxis and even clowns in circuses. These horns have been re-purposed, reshaped, soldered, and polished. They horns are now on display and for sale at:
The two large horns — the trombone and the gramophone — are difficult to pack and ship to they are for local pickup only. The remainder can be sent to you. I have the cowboy horn and the rest are in stock at the Colorado coffee shop. Please call for pricing and availability or stop in for a demo and a great cup of espresso. P.S. Allan, Virginia and I worked together at WebLink Wireless in Dallas. |
||||||||||

|

|

|

|

|

|
| Leavitt Communications |
|
|
|||||||||||||||||||||||||||
6th August 2020
The NHS is set to phase out its outdated communications technologies by 2021 with the launch of a new Clinical Communications Framework.In February 2019 Health and Social Care Secretary, Matt Hancock, ordered the removal of outdated communications from the NHS, such as pagers, for non-emergency communications. NHSX, which aims to drive the digital transformation of health and social care in the UK, has now launched the £3m Clinical Communications Procurement Framework. This agreement between the government and suppliers will allow for faster contracts, whilst helping NHS organisations adopt improved communications technologies and task management tools. Creating a digitised NHSOutdated pagers and communications will be replaced with modern and proven alternatives such as mobile phones and apps, which will help deliver more accurate communications at a much lower cost, as a single pager device can cost up to £400. When proposing the initiative, which aims to help NHS organisations meet the objectives of the NHS Long Term Plan by becoming fully digitised, Hancock said: “Every day, our wonderful NHS staff work incredibly hard in what can be challenging and high-pressured environments. The last thing they need are the frustrations of having to deal with outdated technology — they deserve the very best equipment to help them do their jobs.” The Framework will allow clinicians and NHS Trusts to access these new communication tools under one procurement framework agreement, with 25 suppliers being awarded a place. The website states: ‘The suppliers have been assessed to ensure that they meet all legislative requirements; therefore, no formal tendering is required, saving valuable time and money in the procurement process. The framework contains large national companies but also a healthy number of regional SMEs, and all can showcase their products via the framework, helping buyers to make informed local decisions.’ The framework will run from 3 August 2020 to 3 August 2022, with a potential extension for 12 months, and some pagers will be kept by NHS trusts to help with emergency situations, such as the failure of Wi-Fi. |
| Source: |
|
|||||||||||||||
Motorola Acquires Video Security Solution Provider PelcoMonday, August 03, 2020 Motorola Solutions announced it completed the acquisition of Pelco, a global provider of video security solutions based in Fresno, California. Motorola paid $110 million in cash for Pelco. Pelco designs, develops and distributes end-to-end video technology, including video security cameras and video management system software. The company’s scalable solutions and commitment to service delivery enables customers of all sizes to mitigate risk, increase operational efficiencies and enhance safety. “Video continues to play a more powerful role in enabling safer cities and securing businesses around the world,” said Greg Brown, chairman and CEO, Motorola Solutions. “Pelco’s track record of innovation, internationally recognized brand, global channel and customer installed base enable us to further expand our global footprint with enterprise and public safety customers.” |
| Source: | MissionCritical Communications |
|
Paging Transmitters 150/900 MHz The RFI High Performance Paging Transmitter is designed for use in campus, city, state and country-wide paging systems. Designed for use where reliable simulcast systems where RF signal overlap coverage is critical.
Built-in custom interface for Prism-IPX ipBSC Base Controller for remote control, management and alarm reporting.
Prism-IPX Systems LLC.
11175 Cicero Dr., Alpharetta, GA 30022
|
The Wireless Messaging News
The Board of Advisor members are people with whom I have developed a special rapport, and have met personally. They are not obligated to support the newsletter in any way, except with advice, and maybe an occasional letter to the editor.
Can You Help The Newsletter?
You can help support The Wireless Messaging News by clicking on the PayPal Donate button above. It is not necessary to be a member of PayPal to use this service.
Newspapers generally cost
A donation of $50.00 would certainly help cover a one-year period. If you are wiling and able, please click on the PayPal Donate button above.
|
|||||||||||||||
Va. amateur radio group joins organization
August 5, 2020 A Virginia ARES (Amateur Radio Emergency Service) spokesman announced recently that the organization is now officially a member of the Virginia VOAD (Virginia Voluntary Organizations Active in Disaster). VOAD serves the community in times of disaster, and ARES is an integral part of providing emergency communications. As such, this builds a more effective foundation for serving the needs of community in difficult times. ARES is part of the ARRL, Amateur Radio Relay League, and is responsible for emergency communications using Amateur Radio. |
| Source: | Southside Sentinel |
|
|
| SALCOM |

|
|
|
| PRISM IPX Systems |
| Easy Solutions |
|
Providing Expert Support and Service Contracts for all Glenayre Paging Systems. The GL3000 is the most prolific paging system in the world and Easy Solutions gladly welcomes you to join us in providing reliable support to the paging industry for many more decades in the future. Easy Solutions provides cost effective computer and wireless solutions at affordable prices. We can help in most any situation with your communications systems. We have many years of experience and a vast network of resources to support the industry, your system and an ever changing completive landscape.
Please see our web site for exciting solutions designed specifically for the Wireless Industry. We also maintain a diagnostic lab and provide important repair and replacement parts services for Motorola and Glenayre equipment. Call or
Easy Solutions |
GLENAYRE INFRASTRUCTUREI would like to recommend Easy Solutions for Support of all Glenayre Paging Equipment. This Texas company is owned and operated by Vaughan Bowden. I have known Vaughan for over 35 years. Without going into a long list of his experience and qualifications, let me just say that he was the V.P. of Engineering at PageNet which was—at that time—the largest paging company in the world. So Vaughan knows Paging. GTES is no longer offering support contracts. GTES was the original group from Vancouver that was setup to offer support to customers that wanted to continue with the legacy Glenayre support. Many U.S. customers chose not to use this service because of the price and the original requirement to upgrade to version 8.0 software (which required expensive hardware upgrades, etc.). Most contracts ended as of February 2018. If you are at all concerned about future support of Glenayre products, especially the “king of the hill” the GL3000 paging control terminal, I encourage you to talk to Vaughan about a service contract and please tell him about my recommendation. Click on the image above for more info about advertising here. |
INTERNET Protocol Terminal
The IPT accepts INTERNET or serial messaging using various protocols and can easily convert them to different protocols, or send them out as paging messages. An ideal platform for hospitals, on-site paging applications, or converting legacy systems to modern protocols.
Additional/Optional Features
Prism-IPX Systems LLC.
11175 Cicero Dr., Alpharetta, GA 30022 |
||||||||||||||||||||||||||||||
Emergency PreparednessIndividuals with disabilities should feel as safe and secure in their communities and work environments as individuals without disabilities. Too often, however, the needs of people with disabilities are not considered in emergency planning, despite the fact that the need for such planning has received an increased focus due to recent disasters, both natural and man-made. To help address this disparity, ODEP — through its leadership on the Interagency Coordinating Council on Emergency Preparedness and Individuals with Disabilities — helped develop several resources to assist individuals, organizations, and employers create emergency preparedness plans that take into account the needs of people with disabilities. The following provide more information about emergency preparedness and people with disabilities: Tools and Guidelines
Additional Resources
|
| Source: | US Department of Labor | Office of Disability Employment Policy |
|
Paging Data Receiver PDR-4 The PDR-4 is a multi-function paging data receiver that decodes paging messages and outputs them via the serial port, USB or Ethernet connectors. Designed for use with Prism-IPX ECHO software Message Logging Software to receive messages and log the information for proof of transmission over the air, and if the data was error free.
Prism-IPX Systems LLC.
11175 Cicero Dr., Alpharetta, GA 30022 |
Wireless Network Planners
|
|||||||||||
How Vulnerable Is G.P.S.?An engineering professor has proved—and exploited—its vulnerabilities. By Greg Milner
In the cool, dark hours after midnight on June 20, 2012, Todd Humphreys made the final preparations for his attack on the Global Positioning System. He stood alone in the middle of White Sands Missile Range, in southern New Mexico, sixty miles north of Juárez. All around him were the glowing gypsum dunes of the Chihuahuan Desert. In the distance, the snow-capped San Andres Mountains loomed. On a hill about a kilometre away, his team was gathered around a flat metal box the size of a carry-on suitcase. The electronic machinery inside the box was called a spoofer—a weapon by another name. Soon, a Hornet Mini, a drone-operated helicopter popular with law-enforcement and rescue agencies, was scheduled to appear forty feet above them. Then the spoofer would be put to the test. Humphreys, an engineering professor at the University of Texas at Austin, had been working on this spoofing technology for years, but he was nervous. Witnessing the test that morning was a group of about fifteen officials from the Federal Aviation Administration, the Department of Homeland Security, and the Air Force’s 746th Test Squadron. They were Humphreys’s hosts, but they very much wanted him to fail. His success would mean a major reckoning for the entire G.P.S. system—and, in turn, for the effectiveness of some of the country’s principal military and defense systems. Drones, which rely on G.P.S. to navigate, are an increasingly indispensable part of our security apparatus. Demand for them is growing elsewhere, too. There are now over a million more recreational drones in the sky than there were just four years ago. Sales of high-precision commercial-grade drones—for everything from pipeline inspections to 3-D mapping—increased more than five hundred per cent during the same period. When D.H.S. had first contacted Humphreys a few months earlier, the department was worried about one kind of G.P.S. vulnerability in particular—a disruption to the system called jamming. By transmitting interference, jammers are able to overwhelm a G.P.S. signal and render a drone’s receiver inoperable. There’s no great mystery about how jamming works, but D.H.S. approached Humphreys because it wanted to test the technology in action: Would he be interested in helping with a demonstration? Humphreys accepted the invitation right away, then told the officials that he wanted to focus on a different, more sophisticated threat. In 2011, Iran had made headlines by successfully capturing a C.I.A. drone about a hundred miles from the border with Afghanistan. No one had been sure how the seizure happened: jamming could disorient a drone but not take it over. Humphreys suggested that Iran had succeeded by spoofing the signal—not just interfering with it but actually replacing it with a phantom G.P.S. signal. Tricked into trusting the false system, aircraft could then be commandeered and captured. “Let’s try something more ambitious,” Humphreys told D.H.S. He would see whether he could down a drone. Humphreys, now forty-five, has a gee-whiz fascination with the scientific world that can make him seem younger than he is. He’s earnest and telegenic; you can imagine him hosting a PBS kids’ show that launches a million stem majors. A Utah native, Humphreys had planned to be a patent attorney. But, as an intern at nasa’s Jet Propulsion Laboratory, he listened to a nasa lawyer discussing an upcoming patent and realized that he wanted to be the one inventing things, not approving the inventions. “I thought, Why would I want to be on his side of the table? He’s just taking notes,” Humphreys told me. Humphreys got interested in G.P.S. while he was an engineering grad student at Cornell. He’d been studying software-defined radio—the processing of radio waves by computer software, rather than traditional hardware—and began to wonder whether his research could be used to build a brand-new kind of G.P.S. receiver. G.P.S. is owned by the Department of Defense, operated by the Air Force from a heavily secured room at a base in Colorado, and available for free to anyone in the world. There are twenty-four active G.P.S. satellites, orbiting at twenty thousand kilometres, each one emitting a radio signal that contains a timecode and a description of the satellite’s exact position. By measuring the transmission time of the signal, a G.P.S. receiver determines its distance from the satellite. If the receiver does this simultaneously with the signals of at least four satellites in its line of sight, it can extrapolate its position in three dimensions. During the roughly sixty-seven milliseconds the signal takes to reach us, it grows exceedingly faint. The task of receiving the signal and extracting its informational component is often compared to trying to read using a light bulb in a different city. The core technology of this system has remained the same since the first G.P.S. satellite was launched, in 1977, but its uses have proliferated at an astonishing speed. Although the Air Force oversees satellites that transmit signals, once those signals are broadcast into the world, they belong to everyone. Because G.P.S. is a “passive” system—meaning it merely requires a user to receive a signal, not transmit one—it can handle infinite growth. The number of G.P.S. receivers could double tomorrow without affecting the underlying infrastructure at all. From improving maps to measuring the minute movement of tectonic plates, people have devised more ingenious uses for the G.P.S. signal than the system’s original architects could ever have imagined. Humphreys is one such innovator. Test day at White Sands was the first time Humphreys’s team had used the spoofer outside the lab: because transmitting a fake G.P.S. signal is illegal, they had never even done a full dress rehearsal. For Humphreys, who made money in college as a magician at children’s parties, it felt like premièring a difficult trick without any practice. Around two A.M., the Hornet appeared, hovering forty feet above the missile range. Humphreys spoke a code word into his handheld radio: “Lightning.” Up on the hill, his students switched on the spoofer. Gradually increasing its power, they directed the bogus signal toward the Hornet, which appeared to hesitate in midair, as if encountering an invisible obstacle. The spoofer was, in essence, whispering lies in the drone’s ear, feeding it inaccurate information about its location. Convinced that it had drifted upward, the drone tried to correct, beginning a steep dive toward the desert floor. Just as it was about to crash into the ground, a manual operator grabbed the controls, pulling the Hornet out of its nosedive. Humphreys’s team let out a celebratory whoop over the radio. “We were the only ones clapping,” he told me recently. His hosts looked grim. When Humphreys wasted no time spreading the word about the spoofer’s achievement, they were even more displeased. “I’m told I’ll never be invited back,” he said. “They probably thought I’d do a sleepy presentation in an academic journal. But I was looking to communicate to the world what I thought was an alarming situation.” Since the G.P.S. program began, in 1973, its satellite signals have been a source of controversy. It was the brainchild of an Air Force colonel named Bradford Parkinson, who, disillusioned by the indiscriminate air campaigns of the Vietnam War, imagined G.P.S. as a way to improve the accuracy of precision bombing. Parkinson’s research team designed two versions of the G.P.S. signal, one for civilian use and another, with tighter security protocols and more precise readings, for the military. But when the first G.P.S. satellites were launched, it quickly became clear that the civilian signal was more accurate than its architects had intended. And shrewd scientists discovered that although the military signal’s informational content was heavily encrypted, picking up the radio signal itself wasn’t difficult. It was like gleaning information about a sealed letter by looking at the envelope’s postmark. In the nineties, the Pentagon intentionally corrupted the civilian signal—a practice known as “selective availability”—hoping to thwart terrorists or other bad actors who might otherwise use the signal to launch precision attacks on U.S. assets. But here, too, users found workarounds, and an order from President Bill Clinton, which took effect in 2000, halted the Pentagon’s program. G.P.S. could now be used to its full potential. Soon, the civilian G.P.S. industry was flourishing. By the middle of the decade, Garmin, a leading consumer-G.P.S. company, posted more than $1.6 billion in sales. Car units were proliferating at an annual rate of more than a hundred and forty per cent. The in-car G.P.S. boom gave way, of course, to the smartphone boom: G.P.S. was now something you carried with you always. But the explosive growth of the civilian G.P.S. market also incentivized attempts to corrupt the signal. These days, pocket-sized G.P.S. jammers go for a few hundred dollars each on the Internet and offer an easy out for anyone worried about, say, a surveilling employer. A few years ago, so many truck drivers on the New Jersey Turnpike were using jammers to thwart their bosses’ tracking programs that spillover interference eventually disrupted the G.P.S.-based landing system at Newark Liberty International Airport. G.P.S. is now crucially important for reasons that are unrelated to providing geolocation. Because the G.P.S. clocks are synchronized to within nanoseconds, the network’s signals are used to unify time-dependent systems spread over large areas. G.P.S. time helps bounce calls between cellular towers, regulate power flows in electrical grids, and time-stamp financial trades on the major exchanges. If a spoofer were to feed erroneous information that confused the clocks in even a few nodes of these systems, the damage could be widespread: as time errors multiply, communications systems could fail, wrongly apportioned power flows could result in blackouts, and automated trading programs could yank themselves out of the markets, causing crashes. And those are just a few scenarios. We still have not figured out exactly how to safeguard a technology that is so crucial yet so porous. In 2001, the Department of Transportation released a report warning that G.P.S. could become a “tempting target” for enemies of the U.S. The joint study was the first official acknowledgment that spoofing was a real and significant threat. Humphreys heard about the report while at Cornell. The worst-case spoofing scenario it described seemed like something he could do himself—in fact, like something he could do better himself. Humphreys suspected that these early, crude attempts at spoofing would be easy to detect and thwart. The real threat, he thought, would come from software-defined spoofers, which would be more powerful and more subtle. Traditional receivers rely on G.P.S. chips, which makes them fast but relatively inflexible: you can only change the physical hardware so much. By relying on code instead, software-defined receivers can be infinitely adaptable. Humphreys set about trying to build one. The finished model took years to perfect—“a real beast,” Humphreys called it—partly because he couldn’t perform any real tests on it without breaking the law. He began work on the spoofer at Cornell and finished it with the help of his students at the Radio-navigation Laboratory at the University of Texas. It was this same device, contained in the metal luggage-like box, that took down the Hornet in White Sands. In the months following this début demo, Humphreys kept testing the spoofer, generating an ever-longer list of its capabilities: it could override the timing systems used by mobile-phone networks, electrical grids, and trading programs. The initial good news was that Humphreys probably had one of the only software-defined spoofers in the world. For a few years, the F.B.I. regularly visited his office to insure that he was keeping his creation secure. Humphreys was happy to comply—he didn’t want the technology spreading any more than the F.B.I. did—but, by 2016, code for software-defined G.P.S. spoofers was appearing online, at security conferences, and at hacker conventions. Then, as if to underscore the problem, in February, 2016, a software malfunction at the G.P.S. Master Control Station, in Colorado, caused a thirteen-microsecond clock error in some of the satellites. The glitch took hours to fix, during which the infected satellites spread the timing pathogen across the world. The worst catastrophes were avoided (“World dodges G.P.S. bullet,” proclaimed the trade journal GPS World), but computer networks crashed and digital broadcasts (including the BBC’s) were disrupted. Systems engineers couldn’t help but imagine—and fear—that the nightmare they’d barely avoided could soon become real. The final experiment Humphreys conducted with his spoofer was something of a lark: the owner of a sixty-five-metre super-yacht invited him to try to commandeer its journey across the Mediterranean, from Monaco to Greece. Standing on the upper deck, Humphreys’s team aimed the spoofer at the ship’s antennas, leading the vessel hundreds of metres off course. The experiment was harmless but proved to be a harbinger of some of the most mysterious uses of spoofing. Four years later, in June, 2017, a French oil tanker, the Atria, sailed across the Mediterranean, through the Bosporus strait, and into the Black Sea. As the ship approached the Russian city of Novorossiysk, the captain, Gurvan Le Meur, noticed that the ship’s navigation system appeared to have lost its G.P.S. signal. The signal soon returned, but the position it gave was way off. The Atria was apparently some forty kilometres inland, shipwrecked at the airport in Gelendzhik, a Russian resort town. Le Meur radioed nearby vessels, whose captains reported similar malfunctions in their navigation systems: all in all, twenty other ships had been “transported” to the same inland airport. Meanwhile, something similar had been happening in Moscow—this time to Uber customers, not ship captains. Passengers taking short trips discovered that their accounts were charged for drives all the way to one of the city’s airports, or even to locales thousands of miles away. The activity attracted the interest of the Center for Advanced Defense Studies (C4ADS), a Washington-based think tank focussed on security issues. Using data from ships, which are required by maritime treaties to continuously broadcast their location, researchers discovered that the spoofing problem was much larger than anyone had realized. According to a report released in March of 2019, there were ten thousand spoofing incidents at sea between February 2016 and November 2018, affecting about a thousand and three hundred vessels. Similar data are harder to come by for land vehicles, but C4ADS used heat maps from fitness-tracking smartphone apps to confirm that drivers near the Kremlin and in St. Petersburg encountered similar spoofing. Once they had logged where and when the spoofing incidents occurred, researchers cross-referenced this information with the travel schedule of the Russian President, Vladimir Putin. On a fall afternoon in 2017, six minutes before Putin gave a speech in the coastal town of Bolshoy Kamen, a nearby ship’s G.P.S. coordinates showed it jumping to the airport in Vladivostok. In 2018, when Putin attended the official opening of a bridge across the Kerch Strait, at least twenty-four ships in the area reported their location as Anapa Airport, sixty-five kilometres away. What was going on? It seemed increasingly likely that the President’s security detail was travelling with a portable software-defined spoofer, in the hope of protecting Putin from drone attacks. The strange specificity of the spoofing—the relocation of ships and vehicles to airports—has a cagey explanation. Most drones contain geofencing firmware, which prevents them from entering designated areas, including the world’s major airports. If a drone senses that it’s near an airport, either because it actually is or because spoofed G.P.S. coordinates make it believe that it is, it will either return to its starting point or simply down itself. For one of the world’s most prominent politicians, spoofing may not seem like an unreasonable precaution. In August, 2018, a speech by the Venezuelan President, Nicolás Maduro, was interrupted when a pair of drones detonated above one of Caracas’s largest thoroughfares. A few days later, French secret-service agents destroyed a mysterious drone that flew too close to the summer home of the French President, Emmanuel Macron. But for those who’ve fallen prey to spoofing incidents—the befuddled captains at sea, the overcharged passengers in Moscow—it may be difficult to accept that they are merely collateral in attempts to shield a head of state. And the same technology that might seem like a strategic security system in some circumstances contains within it an ominous potential for subterfuge. Humphreys served as a contributor and adviser for the C4ADS study, and he had a feeling the Black Sea spoofing was even more extensive than the report revealed. To test his hunch, he sought out data from the International Space Station, which collects G.P.S. signals in the upper atmosphere; as it orbited Earth, it would give Humphreys a direct line of sight to the Black Sea. He obtained data from three different orbits in 2018, which he sat down to study that winter, while on sabbatical in his wife’s home town, in the Canary Islands. Unlike the noisy surface of the planet, which is dense with radio signals, the upper atmosphere is a quiet zone, where trespassing frequencies stand out; Humphreys could instantly detect the interference in the Black Sea data. Where were the phantom signals coming from? Humphreys knew that, as the space station passed overhead, the spoofed signal created a kind of Doppler effect. It was a simple clue, familiar to most urban dwellers: Imagine driving a car toward a crime scene that you can hear—sirens, megaphones—but not see. You’ll know when you’re getting close, because of the sudden increase in the pitch of these ambient noises. In much the same way, Humphreys could use the changes in the spoofer’s signal to begin to surmise where it was coming from. When he crunched the numbers, he came up with two possible locations: a forest in Romania and somewhere in Syria. He recalculated using data from another space-station recording and this time concluded that the signal was originating from either the German countryside or, again, somewhere in Syria. When Humphreys checked the exact locations, the two sets of Syrian coordinates were identical: the Khmeimim Airbase, a site on the coast associated with Russian military activity in the country. Further calculations narrowed the source of the interference to a transmitter in the base’s northwest quadrant. The phantom signals Humphreys spotted were unlike anything he’d ever seen before, combining elements of both jamming and spoofing. Like jamming, these signals didn’t transmit actual coordinates. But they were more than just noise—like spoofing, they convinced receivers to recognize false G.P.S. signals. Humphreys calls this “smart jamming” and considers it a new front in the G.P.S.-signal wars. If an authentic signal is a light bulb thousands of miles away, the Syrian fake is a high-wattage spotlight filling your field of vision, blinding you to everything. A commercial jetliner flying thirty thousand feet above a smart jammer would encounter a signal ten billion times more powerful than an ordinary, authentic G.P.S. signal. Even for an airplane just coming over the horizon, with the farthest line-of-sight path to the transmitter, the smart-jammer signal would be five hundred times more powerful than the real one. What Humphreys discovered coming from Khmeimim is the most aggressive G.P.S. disruption device to date. “It’s the most potent example of jamming I’ve ever seen,” Humphreys said. “I call it my Jack Ryan moment.” In January, 2018, the airbase was attacked by a swarm of thirteen drones carrying explosives. Somehow, the attack was thwarted; Humphreys posits that a smart jammer repelled the attack with the assistance of anti-aircraft munitions. G.P.S. interference will likely be a way for America’s foes to fight in conflicts that they could not win conventionally. The civilian uses of G.P.S. have long outnumbered the military applications, but G.P.S. is still part of just about every American weapons system. “This is us getting our first taste of what it’s like to go up against a serious adversary in electronic warfare,” Humphreys said. “I don’t think Russia has shown all its cards yet.” In July of last year, the captain of a container ship registered in the U.S. noticed something strange with his navigation system as he entered the port of Shanghai. The ship’s G.P.S. placed the vessel several kilometres inland. When Humphreys and C4ADS heard of the incident, they doubted that it was an isolated event. “We looked at more data, and, by golly, we saw the same thing popping up in areas around China’s coastline,” Humphreys said. Three hundred other ships had been subject to spoofing in Shanghai on the same day, and thousands of others in the same year. What was unusual about the Shanghai spoofing was that the vessels, rather than being “transported” to the same fake location, were all reporting different coordinates. Further analysis by Bjorn Bergman, at the watchdog group SkyTruth, showed a similar pattern in twenty other locations in China. Humphreys admits that he isn’t sure what explains this new approach to spoofing—or who is behind it. Some have hypothesized that petroleum smugglers and sand thieves may be using the technology to sneak into ports more or less invisibly. Bergman has suggested that the Chinese government is involved in the spoofing; Humphreys says the pattern is widespread enough that it is certainly aware of the activity. Whoever is responsible hasn’t been especially careful—and may not care about being found out. “It really seems like they sent in the junior-varsity team for this one,” Humphreys said. But is there any incentive to work harder? The kind of software-defined spoofer Humphreys revealed at White Sands is now much easier to obtain; you don’t have to be a mastermind to pull off a spoofing attack. And the ease with which amateurs can cause major disruptions should make us worry about what the experts are capable of. Humphreys predicts that the next significant spoofing attacks will target G.P.S.-enabled clocks—and could come from state or non-state actors. “We’re seeing a general consensus that G.P.S. is wonderful, but we’ve got to cut our habit,” Humphreys told me. The signature precision of the system seems to be giving way to blurry, unnerving chaos. But what might a viable alternative look like? Over all, G.P.S. remains a remarkably robust system. Its major vulnerability is the weakness of the signal itself. One fix would be to rebuild the system with a stronger signal by using satellites much closer to us. But this change would require many more satellites to provide global coverage: seven hundred, compared with the current baseline of twenty-four. “Government control of G.P.S. has been a real benefit to all of humanity, the fact that it rains down free from above, with no contract or subscription fees, but I don’t think the G.P.S. program has the funds to expand to low-Earth orbit,” Humphreys said. We may be witnessing the first stage of the death of G.P.S. as we know it. For several years, G.P.S. was the world’s only complete global navigation satellite system. Its only real competition was Russia’s GLONASS, which ranked a distant second. Today, China has implemented the Beidou satellite system, and the European Union has been developing another, called Galileo. But these systems work on similar principles to G.P.S. and have the same vulnerabilities. The answer could eventually be some kind of public-private partnership. Humphreys predicts that companies maintaining hundreds of low-Earth-orbit networks—such as Elon Musk’s SpaceX and Amazon’s Project Kuiper—will eventually become a key component of the G.P.S. ecosystem, picking up the slack in the event of malfunctions or attacks. The new system will be just like G.P.S. as we know it—with one major exception. “It’ll be a pay service, no question,” Humphreys said. “But maybe that’s a decent insurance policy.” |
| Source: | The New Yorker |
Brad Dye, Ron Mercer, Allan Angus, Vic Jackson, and Ira Wiesenfeld are friends and colleagues who work both together and independently, on wireline and wireless communications projects.
Click here
Note: We do not like Patent Trolls, i.e. “a person or company who enforces patent rights against accused infringers in an attempt to collect licensing fees, but does not manufacture products or supply services based upon the patents in question.” We have helped some prominent law firms defend their clients against this annoyance, and would be happy to do some more of this same kind of work. Some people use the title “consultant” when they don't have a real job. We actually do consulting work, and help others based on our many years of experience. “If you would know the road ahead, ask someone who has traveled it.” — Chinese Proverb WHAT IS 5G? 5G is the next generation of wireless networks and promises a mobile experience that's 10x to 100x faster than today's 4G networks. We say the word promise because we're in the early days of 5G. When more smartphones and networks support 5G tech, it will have far-reaching consequences for consumers, from the cars we drive (or that drive us) to the food we eat to the safety of our roads to the ways we shop to the entertainment we share with family and friends. And that doesn't include things we haven't yet imagined because we've never had the capability to unlock those new scenarios. Today, 5G may seem confusing even as it's widely hyped. We're here to help you sort fact from fiction, weed through the acronyms and jargon, and figure out when and how 5G can change the way you live. And we'll keep you from getting caught up in hyperbole — and empty promises. [ source ] |
Remote AB Switches ABX-1 switches are often used at remote transmitter sites to convert from old, outdated and unsupported controllers to the new modern Prism-IPX ipBSC base station controllers. Remotely switch to new controllers with GUI commands. ABX-1
ABX-3 switches are widely used for enabling or disabling remote equipment and switching I/O connections between redundant messaging systems. ABX-3
Common Features:
Prism-IPX Systems LLC.
11175 Cicero Dr., Alpharetta, GA 30022 |
| Leavitt Communications |
|
|||||||
| Inside Towers Newsletter |
|
Strong Tower Market Sways FCC to Nix Rules on Access to FM, TV Antenna SitesThe FCC yesterday eliminated rules regarding access to FM and TV broadcast antenna sites, thanks in part to a robust tower market. The agency said the rules no longer serve any practical purpose given the “significant broadcast infrastructure development” that has occurred since adopted 75 years ago. Sections 73.239 and 73.635 of the Commission’s rules prohibit the grant or renewal of an FM or TV broadcast license “to any person who owns, leases, or controls a particular site which is peculiarly suitable” for such broadcasting in a particular area, if the site is not available for use by other such licensees, no other comparable site is available in the area, and the exclusive use of the site would unduly limit the number of such stations that can be licensed or unduly restrict competition among those stations. The rules were adopted during a time when FM and TV broadcasting were emerging industries, and the need to preserve materials for the U.S. military effort in World War II had led the Commission to freeze new broadcast station construction. Since that time, the broadcast market has grown significantly with a corresponding increase in the number of available antenna sites. This is made possible, in part, by the ability to co-locate broadcasters and other providers at a single site and a mature independent communications tower industry that owns and leases tower space to broadcasters. In 2019, the Commission asked for input on whether the rules should be modified or eliminated. The agency also asked to what extent broadcasters own their own towers and what extent eliminating the rules would have on the broadcast tower landscape. Only two members of the public filed comments. The agency concluded eliminating the rules is appropriate for four reasons. First, the apparent rationale for these rules—promoting a fledgling broadcast industry and preserving scarce industrial resources—no longer applies in today’s marketplace. Also, the current trend toward co-location of communications towers on antenna farms and the widespread availability of tower capacity for lease from numerous tower companies make it less likely that a suitable site will be wholly unavailable to a broadcaster seeking to serve a community. Second, publicly available information shows that the communications tower market is dominated by entities that do not hold broadcast licenses, and there is no indication that their broadcast lessees have the intent or ability to restrict these tower owners from denying access to the broadcast lessees’ competitors. Third, the current rules apply only in extremely limited circumstances, and no broadcaster claims that these rules are needed to secure access to suitable sites. Finally, the FCC concluded that keeping rules that have little applicability to the broadcast landscape is a waste of Commission time and resources. “Simply put, based on our expert judgment and the lack of record received, we find that these 75-year-old rules have outlived their utility,” stated the agency. |
| Source: | Inside Towers newsletter |
Courtesy of the editor of
Inside Towers
Jim Fryer.
Inside Towers is a daily newsletter by subscription. |
| BloostonLaw Newsletter |
FCC Updates Lifeline Minimum Service Standards, Index Budget AmountOn July 31, the FCC issued a Public Notice announcing the newly calculated minimum service standards for fixed and mobile broadband. These standards will take effect on December 1, 2020. First, the Lifeline minimum service standard for fixed broadband speed will be 25 Mbps downstream and 3 Mbps upstream, with a minimum usage of 1024 GB per month. The Lifeline minimum service standard for mobile broadband data capacity will increase to 11.75 GB per month, and the minimum speed remains 3G mobile technology. We note, however, that the FCC has proposed changes to this calculation that would result in a new capacity of 4.5 GB per month instead of 11.75. See the article below for more. Finally, the Lifeline minimum service standard for mobile voice service will remain unchanged, at 1,000 minutes per month, and the indexed budget for the calendar year beginning January 1, 2021 will be $2,428,227,364. BloostonLaw Contacts: Ben Dickens, Gerry Duffy, Mary Sisak, and Sal Taillefer. HeadlinesWhite House Withdraws Commissioner O’Rielly RenominationOn August 3, Reuters broke the news that the White House has withdrawn the nomination of Commissioner Michael O’Rielly to a second term at the FCC. The announcement came shortly after U.S. Sen. Jim Inhofe (R-Okla.) announced that he had placed a hold on the nomination until Commissioner O’Rielly committed to vote to overturn the Ligado Order. As we reported in a previous edition of the BloostonLaw Telecom Update, on April 19, 2020 the FCC granted satellite service provider Ligado’s application to deploy a low-power terrestrial nationwide network in the L-Band, that will primarily support 5G and Internet of Things services. Sen. Inhofe has been active in opposing the Ligado application leading up to and even after its grant, based on concerns by the Department of Defense and several other government agencies and industry members that Ligado will cause interference to GPS. It is unclear whether Sen. Inhofe’s announcement played the withdrawal. According to Reuters, the White House declined to comment. BloostonLaw Contacts: Ben Dickens, Gerry Duffy, and John Prendergast. Chairman Pai Circulates Order Increasing Minimum Standard for Lifeline Mobile BroadbandOn July 30, FCC Chairman Ajit Pai circulated an order to his colleagues that would improve the way the FCC calculates annual updates to the minimum service standard for mobile broadband service provided through the Lifeline program, according to a Press Release. Specifically, the Press Release indicates that the draft order would revise the Commission’s existing methodology to “ensure predictable, reasonable yearly updates to the standard so that Lifeline subscribers can receive robust yet affordable mobile broadband service.” Under the revised methodology, the Lifeline program’s minimum service standard for mobile broadband data capacity would increase, effective December 1, 2020, from 3 GB to 4.5 GB per month. Absent this reform, the standard would increase from 3 GB to 11.75 GB per month. “The Lifeline program plays an important role in ensuring that low-income Americans have access to affordable broadband service,” Chairman Pai said. “And as the communications marketplace continually evolves, it’s critical that minimum standards for Lifeline service increase so that Lifeline subscribers do not receive second-class service compared to other consumers. But the formula the FCC adopted back in 2016 to update the minimum standard for Lifeline mobile broadband data capacity is flawed. It results in drastic year-over-year increases that could impact the ability of Lifeline carriers to continue providing affordable service. Last year, the first time the formula was applied, the current Commission had to step in to avoid this outcome. Now, I’ve circulated an order that would permanently clean up the mess caused by the 2016 order. I hope that my colleagues will vote for this order, which will provide much-needed certainty to Lifeline subscribers and providers alike.” BloostonLaw Contacts: John Prendergast, Cary Mitchell, and Sal Taillefer. FCC Adopts Declaratory Ruling to Clarify Pole Attachment RulesOn July 29, the FCC adopted a Declaratory Ruling to address a Petition for Declaratory Ruling filed by CTIA in September of 2019, concerning pole attachment rules. Specifically, the FCC clarified that: (1) the imposition of a “blanket ban” by a utility on attachments to any portion of a utility pole is inconsistent with the federal requirement that a “denial of access . . . be specific” to a particular request; and (2) while utilities and attachers have the flexibility to negotiate terms in their pole attachment agreements that differ from the requirements in the Commission’s rules, a utility cannot use its significant negotiating leverage to require an attacher to give up rights to which the attacher is entitled under the rules without the attacher obtaining a corresponding benefit. The Declaratory Ruling deviates substantially from the relief CTIA initially sought in its petition. There, CTIA asked the FCC to clarify its rules by: (1) declaring that the term “pole” includes light poles and that utilities must afford nondiscriminatory access to light poles at rates, terms, and conditions; (2) affirming that utilities may not impose blanket prohibitions on access to any portions of their poles; and (3) declaring that utilities cannot ask providers to accept terms and conditions that are inconsistent with the Commission’s rules. As a threshold matter, the FCC declined to address CTIA’s request concerning light poles. As a result, that issue remains pending. Presumably, further FCC action is forthcoming. Regarding CTIA’s request for clarification on blanket prohibitions, the FCC found that despite its statement in 2011 that “[b]lanket prohibitions are not permitted under the Commission’s [pole attachment] rules,” the record nevertheless showed that many pole owners were continuing to deny access summarily to all or part of poles, without giving reasons for denying access that are specific to the pole or attachment. Therefore, the FCC clarified that such blanket prohibitions are themselves prohibited. The FCC did not, however, completely agree with CTIA’s request concerning deviations from the Commission’s rules. While CTIA sought clarification that any deviation from the rules was not permitted, the FCC found only that attachers are entitled to a corresponding benefit if the parties agree to such deviation. According to the FCC, it has made (and continues to support) “several statements aimed at preserving the ability of utilities and attachers to reach mutually-bargained-for solutions (which may differ from the pole attachment rules) in negotiating their pole attachment agreements.” BloostonLaw Contacts: John Prendergast and Cary Mitchell. Bidding in 3.5 GHz CBRS Auction Nears $2B MarkGross proceeds in the FCC’s auction for Priority Access Licenses (PALs) in the 3.5 GHz shared use Citizens Broadband Radio Services (CBRS) band (Auction 105) are approaching $2 billion in the second full week of bidding. There has been high demand for PALs in major markets like LA (20 blocks excess demand at a posted price of almost $20 million/block), San Diego (16 blocks excess demand at a posted price of over $6.1 million) and New York City (12 blocks excess demand for New York, Kings County and Queens County and an aggregate price of posted price exceeding $12 million), as well as in many rural counties. On Wednesday, after Round 25 bids were tallied, Auction 105 gross proceeds stood at $1.83 billion. Prices are continuing to rise for PALs in 481 out of 3,233 counties nationwide, or 15% of counties. PAL prices are steady in 85% of counties. Analysts have estimated that total proceeds from Auction 105 could exceed $3 billion. There are 271 qualified bidders vying for the flexible use PALs and the auction has gained attention from numerous entrepreneurs and WISPs, as well as traditional players. The tiered sharing framework gives PAL licensees priority over General Authorized Access (GAA) users in the band, which is shared with first priority federal incumbents. GAA users are allowed access to PAL spectrum in areas where it is not being used by PAL licensees. Bidding in Auction 105 could extend into September, especially if bidders in the larger markets begin to focus on smaller and rural areas in later bidding rounds. The FCC can also speed the pace of bidding by increasing the number of bidding rounds per day (currently at 3 rounds), and can help bring the auction to a close by requiring bidders to maintain a minimum activity requirement of 100% (the current activity requirement is 95%, where it has been since the beginning of the auction). Mid-band spectrum is thought to be a valuable resource for 5G deployment among other purposes, and Auction 105 is offering up 70 MHz for Priority Access Licensees. Up to 80 MHz of mid-band spectrum is available for shared use by GAA users. The FCC has set December 8 as its target date for the start of bidding in the upcoming C-Band auction (Auction 107), offering 280 MHz of mid-band spectrum for 5G. BloostonLaw Contacts: Cary Mitchell and John Prendergast. Law and RegulationFCC Extends 2.5 GHz Rural Tribal Priority Window to September 2On July 31, the FCC extended the Rural Tribal Priority Window for 2.5 GHz spectrum applications by 30 days in light of the COVID-19 pandemic. This window opened on February 3, 2020, and as a result of today’s action, eligible Tribal entities can continue to apply for licenses to use currently unassigned 2.5 GHz spectrum over their rural Tribal lands until 6:00 pm EDT on September 2, 2020. After the Rural Tribal Priority Window closes, FCC staff will review and process the applications and prepare for a commercial auction of any remaining unassigned 2.5 GHz spectrum. “Under my leadership, the Commission for the first time ever is giving Tribes priority access to spectrum. I’m pleased to see that we’ve already received a large number of applications during the Rural Tribal Priority Window. And due to the COVID-19 pandemic, I believe that it is appropriate to extend the application deadline by 30 days,” said FCC Chairman Ajit Pai. “By contrast, a much longer extension would substantially delay our award of licenses to Tribal entities and thus delay their ability to use this spectrum to connect those consumers living on Tribal lands. Moreover, in light of the simplified application process as well as the extensive outreach done by Commission staff, a lengthy extension of the deadline is unnecessary, as evidenced by the large number of applications we’ve already received.” BloostonLaw Contacts: John Prendergast and Cary Mitchell. Comments on Fourth Robocall FNPRM Due August 31On July 31, the FCC published in the Federal Register its Fourth Further Notice of Proposed Rulemaking in which it proposes additional steps to implement the TRACED Act and protect consumers from illegal calls, while also providing transparency and effective redress to legitimate callers. Comments are due August 31, 2020, and reply comments are due September 29, 2020. As we reported in a previous edition of the BloostonLaw Telecom Update, the FCC adopted a Third Report and Order and Fourth Further Notice of Proposed Rulemaking at its July Open Meeting. The Further Notice portion of the document seeks comment on whether to obligate phone companies to better police their networks against illegal calls, and whether to require them to provide information about blocked calls to consumers for free. In addition, the Further Notice seeks comment on notification and effective redress mechanisms for callers when their calls are blocked, and on whether measures are necessary to address the mislabeling of calls. The Third Report and Order portion of the document adopted two safe harbors from liability for the unintended or inadvertent blocking of wanted calls: the first safe harbor protects phone companies that use reasonable analytics, including caller ID authentication information, to identify and block illegal or unwanted calls from liability; the second safe harbor protects providers that block call traffic from bad actor upstream voice service providers that pass illegal or unwanted calls along to other providers, when those upstream providers have been notified but fail to take action to stop these calls. BloostonLaw Contacts: Gerry Duffy, Mary Sisak, and Sal Taillefer. 911 Reliability Certification System Available; Filings Due October 15On July 30, the FCC issued a Public Notice announcing that its 911 Reliability Certification System is now open for filing annual reliability certifications, which are not due until October 15, 2020. The Commission’s online portal can be found at https://apps2.fcc.gov/rcs911/. The Commission’s rules require Covered 911 Service Providers, which are defined as entities that “[p]rovide[] 911, E911, or NG911 capabilities such as call routing, automatic location information (ALI), automatic number identification (ANI), or the functional equivalent of those capabilities, directly to a public safety answering point (PSAP), statewide default answering point, or appropriate local emergency authority,” or that “[o]perate[] one or more central offices that directly serve a PSAP,” are required certify that they have taken reasonable measures to provide reliable 911 service with respect to three substantive requirements: (i) 911 circuit diversity; (ii) central office backup power; and (iii) diverse network monitoring. BloostonLaw Contacts: Mary Sisak and Sal Taillefer. IndustryFCC Announces New Speed Test AppOn August 3, the FCC issued a Press Release announcing that it has released an updated version of its FCC Speed Test app, in order to provide consumers with tools to evaluate how well their mobile broadband connections are performing. Like its predecessor, the updated app allows users to test their cellular and Wi-Fi network performance for download and upload speed, latency, jitter, and packet loss. While the app reportedly collects no personal or uniquely identifiable information, it does collect the speed test data, and the raw data sets are available for public download on the FCC’s webpage. Now included is the latest data for mobile measurements conducted by the FCC Speed Test App through the second quarter of 2020. The latest data set can be found here: https://www.fcc.gov/reports-research/reports/measuring-broadband-america/measuring-broadband-america-mobile-data. DeadlinesAUGUST 1: FCC FORM 502, NUMBER UTILIZATION AND FORECAST REPORT: Any wireless or wireline carrier (including paging companies) that have received number blocks--including 100, 1,000, or 10,000 number blocks--from the North American Numbering Plan Administrator (NANPA), a Pooling Administrator, or from another carrier, must file Form 502 by August 1. Carriers porting numbers for the purpose of transferring an established customer’s service to another service provider must also report, but the carrier receiving numbers through porting does not. Resold services should also be treated like ported numbers, meaning the carrier transferring the resold service to another carrier is required to report those numbers but the carrier receiving such numbers should not report them. Reporting carriers file utilization and forecast reports semiannually on or before February 1 for the preceding six-month reporting period ending December 31, and on or before August 1 for the preceding six-month reporting period ending June 30. BloostonLaw Contacts: Ben Dickens and Gerry Duffy. AUGUST 1: Live 911 Call Data Reports – Non-Nationwide Providers that do not provide coverage in any of the Test Cities must collect and report aggregate data based on the largest county within its footprint to APCO, NENA, and NASNA on the location technologies used for live 911 calls in those areas. Clients should obtain spreadsheets with their company’s compliance data from their E911 service provider (e.g., Intrado / West). BloostonLaw Contact: Cary Mitchell. AUGUST 29: COPYRIGHT STATEMENT OF ACCOUNTS. The Copyright Statement of Accounts form plus royalty payment for the first half of year is due to be filed August 29 at the Library of Congress’ Copyright Office by cable TV service providers. BloostonLaw contact: Gerry Duffy. SEPTEMBER 1: FCC FORM 477, LOCAL COMPETITION AND BROADBAND REPORTING FORM. Three types of entities must file this form.
BloostonLaw Contacts: Ben Dickens and Gerry Duffy. SEPTEMBER 30: FCC FORM 396-C, MVPD EEO PROGRAM REPORTING FORM. Each year on September 30, multi-channel video program distributors (“MVPDs”) must file with the FCC an FCC Form 396-C, Multi-Channel Video Programming Distributor EEO Program Annual Report, for employment units with six or more full-time employees. Users must access the FCC’s electronic filing system via the Internet in order to submit the form; it will not be accepted if filed on paper unless accompanied by an appropriate request for waiver of the electronic filing requirement. Certain MVPDs also will be required to complete portions of the Supplemental Investigation Sheet (“SIS”) located at the end of the Form. These MVPDs are specifically identified in a Public Notice each year by the FCC. BloostonLaw Contacts: Gerry Duffy and Sal Taillefer. OCTOBER 15: 911 RELIABILITY CERTIFICATION. Covered 911 Service Providers, which are defined as entities that “[p]rovide[] 911, E911, or NG911 capabilities such as call routing, automatic location information (ALI), automatic number identification (ANI), or the functional equivalent of those capabilities, directly to a public safety answering point (PSAP), statewide default answering point, or appropriate local emergency authority,” or that “[o]perate[] one or more central offices that directly serve a PSAP,” are required certify that they have taken reasonable measures to provide reliable 911 service with respect to three substantive requirements: (i) 911 circuit diversity; (ii) central office backup power; and (iii) diverse network monitoring by October 15. Certifications must be made through the FCC’s portal. BloostonLaw Contacts: Mary Sisak and Sal Taillefer. Calendar At-a-GlanceAugust September October
|
|
||||||
| LETTERS TO THE EDITOR |
Brad: Glad you are staying well. Keep it up. The newsletter is a GEM. Will you please let your readers know I have 6 Sonic PTX150 VHF paging transmitters available. They are 100 watt, POCSAG/FLEX™ capable and covers 138-174 MHz. Power cords are included. They were removed WORKING from a county paging system and are guaranteed by me. $1,425.00 each. Phil
Please contact Phil directly. The newsletter will receive a 10% to 15% commission on any sales made. (On the honor system — no contract.) |
|||||||||||||||||||||||
| THIS WEEK'S TECHNICAL VIDEO |
“Sunshine”Avalon Jazz Band |
| Source: | YouTube |
 Best regards,  Newsletter Editor 73 DE K9IQY Licensed since 1957 |
Current member or former member of these organizations. | ||||
|
The National
Rifle Association |
MENSA MEMBER
|
A Public Library of
Paging and Wireless Messaging Information |
Wireless
 Messaging |
||
|
Critical Messaging
 Association |
European Mobile Messaging Association
Former Board Member |
ZP5TQ
 Radio Club of Paraguay |
Quarter Century
Wireless Association |
|
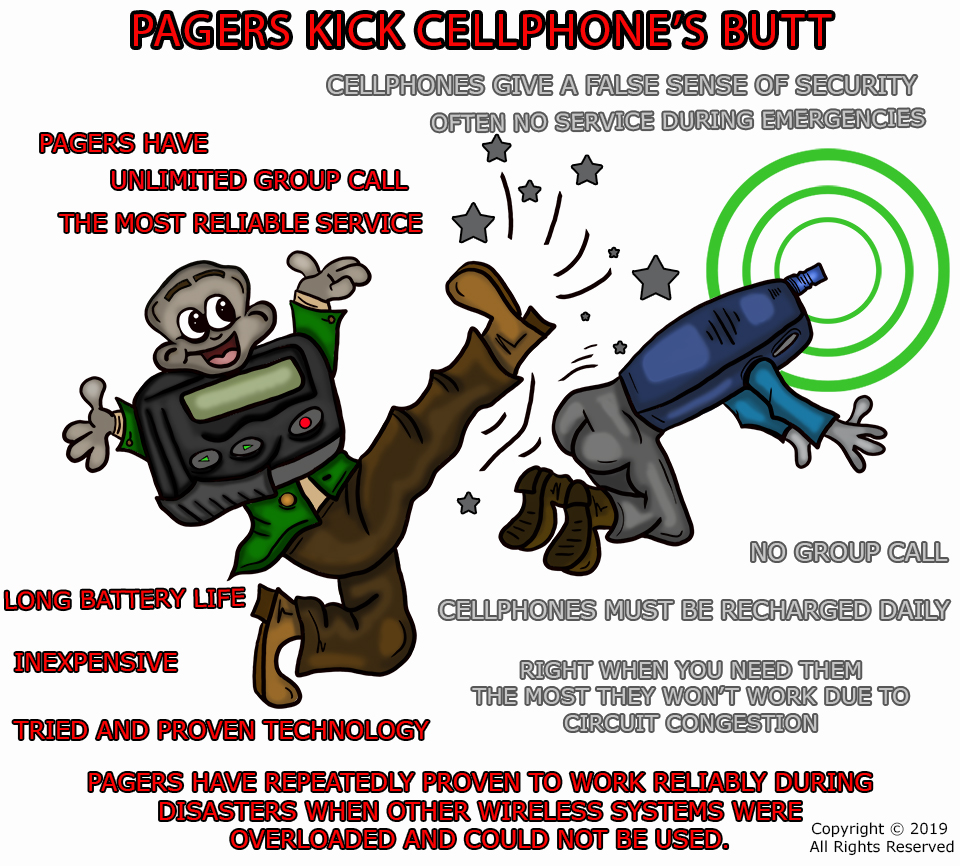
Back To Paging

Still The Most Reliable Wireless Protocol For Emergencies! |
American Association
of Woodturners |
U.S. Navy
 Radioman |
U.S. Navy Radioman  Second Class Petty Officer |
Boy Scouts of America
 National Honor Society |
Creator of the
 Paging Wheel of Fortune |
National Skeet
 Shooting Association |
Institute Electrical and

Electronics Engineers |
American Radio 
Relay League |
The Radio Club

of America |
Life is good!
|
|
|
CONTACT INFO & LINKS
|
Amateur Radio
|
VETERAN
 United States Navy |
|||
| Home Page | Directory | Consulting | Newsletters | Free Subscription | Products | Reference | Glossary | Send e-mail |