![]()
WIRELESS
MESSAGING
NEWS
![]()
MENSA
MEMBER
|
|
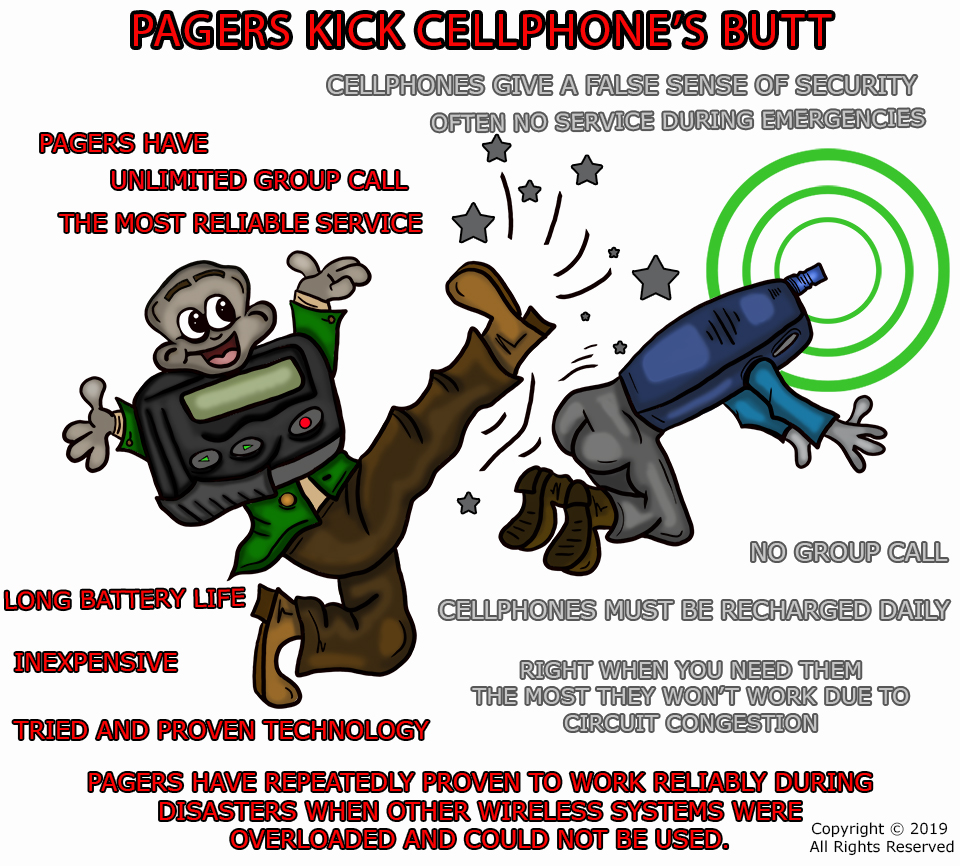 |
|
Do you think Paging is obsolete? It is a common misconception that paging technology has been superseded by newer and better means of wireless communication. This is far from the truth. Jim Nelson, President & CEO of Prism-IPX Systems, has written an excellent paper explaining why paging continues to be the right choice for critical messaging. |
IMPORTANT “Is Paging Going Away?”
With the help of Angelo Saccoccia and his team at Swissphone we now have this great report on the health and wellbeing of Paging available in French and German. Let's work together to get this important message circulated to a wider audience. Dr. Dietmar Gollnick and his staff at e*Message in Berlin have contributed some minor but valuable revisions to the German translation. Volunteers needed for translations into other languages. |

Directory
A Directory of Paging Service Providers is under perpetual construction. Please click on the "Directory" button above. Carriers that want to be listed, need only submit the information about their companies via e-mail. To submit your company's information, just click here ![]() and send me the information.
and send me the information.
Hello, I am Brad Dye. Welcome to my homepage — THE PAGING INFORMATION RESOURCE — a collection of articles about Radio Paging, Wireless Messaging, and Wireless Data communications.
If you are involved in Wireless Messaging. Paging, or Wireless Telemetry, you will find many items of interest on this web site. Recommended wireless products and services can be located by clicking on the PRODUCTS button above. Come on in and browse around. There are over 10,000 files on this site. I hope you find it interesting and helpful. The good stuff about Wireless Messaging, Telemetry, and Paging is in the MAIN TOPICS section.
More about Paging's advantages here ![]()

| The Wireless Messaging News |
A new issue of the Wireless Messaging News gets posted on the web each week. A notification goes out by e-mail to subscribers on most Fridays around noon central-US time. The notification message has a link to the newsletter on the Internet. There is no charge for subscription and there are no membership restrictions. The newsletter is supported by advertising. Readers are a very select group of wireless industry professionals, and include the senior managers of many of the world's major paging and wireless data companies. There is an even mix of operations managers, marketing people, and engineers, so I try to include items of interest to all three groups. This newsletter is independent of any trade association. |
|
WIRELESS |
 |
It's all about staying up-to-date with business trends and technology. If you would like to subscribe to the newsletter just fill in the blanks in the form below, and then click on the “Subscribe” bar. |
|
* required field |
For past issues, please click on the NEWSLETTERS button at the top of this page. I will not share your e-mail address with anyone, so you don't have to worry about getting a lot of junk mail if you sign up for this newsletter. You will only receive the newsletter once a week and you can choose to unsubscribe at any time. Once-in-a-while I may send out a news bulletin or a special advisory about a trade show.
![]()
For information about advertising in the newsletter and on this web site just click here:


To read the latest newsletter click on this button:


Back issues are available here: Newsletters
Advertise in the newsletter.
If you would like to help keep the Paging Information Resource and the Wireless Messaging Newsletter going, you can contribute by clicking on the PayPal Donate button below. You don't have to be a member of PayPal to use their service.











 I work in the radio paging industry. Some of the information included on these pages is personal — about my hobbies and family for example — and some of it is professional. A lot of it is made up of papers about Radio Paging that I wrote several years ago while working for Motorola. I add new information about once a week and occasionally throw away things that are no longer of interest. All of the information here is in the public domain and you are free to use it as you wish. Of course, neither I, nor my former employers, accept any responsibility for its accuracy. I can't guarantee that you will become rich and famous if you follow my advice—some do and some don't. The ideas and opinions expressed here are my own, except for those papers obviously written by others. This site is a community effort.
I work in the radio paging industry. Some of the information included on these pages is personal — about my hobbies and family for example — and some of it is professional. A lot of it is made up of papers about Radio Paging that I wrote several years ago while working for Motorola. I add new information about once a week and occasionally throw away things that are no longer of interest. All of the information here is in the public domain and you are free to use it as you wish. Of course, neither I, nor my former employers, accept any responsibility for its accuracy. I can't guarantee that you will become rich and famous if you follow my advice—some do and some don't. The ideas and opinions expressed here are my own, except for those papers obviously written by others. This site is a community effort.





 Wireless Messaging and Paging Information Search Engine
Wireless Messaging and Paging Information Search Engine